As with every major WikiLeakS.org media frenzy in the past, the WikiLeaKS.org web servers cannot cope with the high demand caused by their release of (name censored) US military SIGACT (Significant Action) reports.
Yet again they have chosen to create a dedicated website for these "Iraq War Diaries" (http://warlogs.wikileaks.org/) and the main http://wikileaks.org website untrustworthy and misspelled message that it is "currently underoing scheduled maintenance" (it has been so for over a week)
Also, predictably, we are getting blog searches for WikiLeakS.org documents even though it is clearly stated that none of them are here.
We are also getting irate emails , including, and a couple of death threats from people who claim to be supporters of US military, who cannot aim properly on the internet, thereby breaking the Acceptable Use terms and conditions of their Internet Service Provider contracts and several criminal laws.
is it any wonder that there have been so many unnecessary "blue on blue" / "friendly fire" attacks and casualties ?
Yet again they have chosen to create a dedicated website for these "Iraq War Diaries" (http://warlogs.wikileaks.org/) and the main http://wikileaks.org website untrustworthy and misspelled message that it is "currently underoing scheduled maintenance" (it has been so for over a week)
Also, predictably, we are getting blog searches for WikiLeakS.org documents even though it is clearly stated that none of them are here.
We are also getting irate emails , including, and a couple of death threats from people who claim to be supporters of US military, who cannot aim properly on the internet, thereby breaking the Acceptable Use terms and conditions of their Internet Service Provider contracts and several criminal laws.
is it any wonder that there have been so many unnecessary "blue on blue" / "friendly fire" attacks and casualties ?
Der Speigel reports:that "Daniel Schmitt", now named in public as Daniel Domscheit-Berg, who has shared platforms with Julain Assange as the (English speaking) German spokesman for the WikiLeakS.org project, especially at the annual Chaos Computer Congress, is set to resign:
Will the people who are deeply unhappy with it start a new rival project, with their experience of WikiLeakS.org success and failures, or are they so fed up with it that they will go back to their normal lives and concentrate on their many other pro bono and voluntary activities instead ?
Internal Strife at WikiLeaks - German Spokesman Says He Will Leave WebsWill the WikiLeaKs.org project now collapse or will it change to become more transparent and accountable ?
A dispute has broken out within the leadership of WikiLeaks, the website known for publishing classified documents including the Afghanistan war logs. In an interview with SPIEGEL, WikiLeaks' German spokesman has said he will leave the organization as a result of rows with founder Julian Assange.
In a SPIEGEL interview to be published in the next issue, Daniel Schmitt, the German spokesman for WikiLeaks discusses the deficiencies within the whistleblower platform, criticizes internal fighting in the organization and announces his resignation.
"We all had an insane amount of stress in recent months," he told SPIEGEL. "A few mistakes happened, which is OK, as long as people learn from them. For that to happen, though, one has to admit them. We have lost the faith that we are all pulling together."
In recent months WikiLeaks landed a string of spectacular coups, including the publication of 77,000 secret United States military logs from the war in Afghanistan. Schmitt criticized the fact that the platform has been too focused on large projects and that, in doing so, it has neglected smaller, national documents.
He also blamed that on WikiLeaks founder Julian Assange. "I tried again and again to push for that, but Julian Assange reacted to any criticism with the allegation that I was disobedient to him and unloyal to the project." He said he had come to disagreements with Assange and that other co-workers were also unhappy.
"There is a lot of displeasure there and some others, like me, will pull out," he told SPIEGEL. Out of fears of attacks, WikiLeaks' German spokesman had called himself Daniel Schmitt up until now. In his SPIEGEL interview, however, he revealed his real name for the first time: Daniel Domscheit-Berg.
Will the people who are deeply unhappy with it start a new rival project, with their experience of WikiLeakS.org success and failures, or are they so fed up with it that they will go back to their normal lives and concentrate on their many other pro bono and voluntary activities instead ?
We ave previously commented that WkiLeakS.org, or similar organisations, actually require the same sort off "tax haven" and "tax avoidance" techniques employed by the Private Banking industry which they so gleefully try to expose the details of "for maximum political effect".
The Wall Street Journal has been "investigating", without actually revealing the details of any of the front companies and foundations, apart from some of the ones which have appeared on the WikiLeakS.org financial contributions pages. It is is disappointing that a financial sector newspaper like the Wall Street Journal, cannot find, or will not publish, any more details, other than those provided by Julian Assange.
Have these been verified in any way e.g. is WikiLeakS.org really registered as a library in Australia ?
No "tax evasion" / "tax avoidance" trust funds and front companies registered in tax havens are "operational concerns" either, but that does not prevent various tax authorities going after them and their beneficiaries.
The other big risks to rich financial donors involve the horrendously complicated and ineffective (in terms of catching real criminals and terrorists) anti-money laundering regulations and investigations, which various government bureaucracies have imposed on the financial industry, especially for foreign money transfers.
How does WikiLeakS.org provide any protection to financial donors in such cases ?
Note also that another online money payment system which WikiLeakS.org has used during their dispute with PayPal, called TipIt.to seems to have gone "tits up" at the end of February 2010 due to "fraudulent transactions"
http://blog.tipit.to/2010/04/gesloten-voor-preventie-%E2%80%94%C2%A0closed-for-prevention/
The Wall Street Journal has been "investigating", without actually revealing the details of any of the front companies and foundations, apart from some of the ones which have appeared on the WikiLeakS.org financial contributions pages. It is is disappointing that a financial sector newspaper like the Wall Street Journal, cannot find, or will not publish, any more details, other than those provided by Julian Assange.
Have these been verified in any way e.g. is WikiLeakS.org really registered as a library in Australia ?
How WikiLeaks Keeps Its Funding SecretThis lack of financial transparency is one of the major failings of the WikiLeakS.org project.
By JEANNE WHALEN and DAVID CRAWFORD
The controversial website WikiLeaks, which argues the cause of openness in leaking classified or confidential documents, has set up an elaborate global financial network to protect a big secret of its own--its funding.
Some governments and corporations angered by the site's publications have already sued WikiLeaks or blocked access to it, and the group fears that its money and infrastructure could be targeted further, founder Julian Assange said in an interview in London shortly after publishing 76,000 classified U.S. documents about the war in Afghanistan in July. The move sparked international controversy and put WikiLeaks in the spotlight.
In response, the site has established a complex system for collecting and disbursing its donations to obscure their origin and use, Mr. Assange said. Anchoring the system is a foundation in Germany established in memory of a computer hacker who died in 2001.
WikiLeaks's financial stability has waxed and waned during its short history. The site shut down briefly late last year, citing a lack of funds, but Mr. Assange said the group has raised about $1 million since the start of 2010.
WikiLeaks's lack of financial transparency stands in contrast to the total transparency it seeks from governments and corporations.
"It's very hard work to run an organization, let alone one that's constantly being spied upon and sued," Mr. Assange said in the The controversial website WikiLeaks, which argues the cause of openness in leaking classified or confidential documents, has set up an elaborate global financial network to protect a big secret of its own--its funding.Nonsense ! There are several Islamic Charities which not only have been sued, but have subjected to anti-terrorism investigations and have had their financial assets frozen, even though they have never been "operational concerns" either.
Some governments and corporations angered by the site's publications have already sued WikiLeaks or blocked access to it, and the group fears that its money and infrastructure could be targeted further, founder Julian Assange said in an interview in London shortly after publishing 76,000 classified U.S. documents about the war in Afghanistan in July. The move sparked international controversy and put WikiLeaks in the spotlight.
In response, the site has established a complex system for collecting and disbursing its donations to obscure their origin and use, Mr. Assange said. Anchoring the system is a foundation in Germany established in memory of a computer hacker who died in 2001.
WikiLeaks's financial stability has waxed and waned during its short history. The site shut down briefly late last year, citing a lack of funds, but Mr. Assange said the group has raised about $1 million since the start of 2010.
WikiLeaks's lack of financial transparency stands in contrast to the total transparency it seeks from governments and corporations.
"It's very hard work to run an organization, let alone one that's constantly being spied upon and sued," Mr. Assange said in the interview. "Judicial decisions can have an effect on an organization's operation. ... We can't have our cash flow constrained entirely," he said.
Among the cases WikiLeaks has faced, the Swiss bank Julius Baer & Co. in 2008 sued for damages in federal court in California, alleging that the site had published stolen bank documents. The court ordered the disabling of the wikileaks.org domain name, but the bank withdrew its lawsuit after civil-rights advocates protested.
Though Mr. Assange declined to name donors or certain companies through which donations flow, he provided some insight into the funding structure that allows the group to operate.
The linchpin of WikiLeaks's financial network is Germany's Wau Holland Foundation. WikiLeaks encourages donors to contribute to its account at the foundation, which under German law can't publicly disclose the names of donors. Because the foundation "is not an operational concern, it can't be sued for doing anything. So the donors' money is protected, in other words, from lawsuits," Mr. Assange said.
No "tax evasion" / "tax avoidance" trust funds and front companies registered in tax havens are "operational concerns" either, but that does not prevent various tax authorities going after them and their beneficiaries.
The German foundation is only one piece of the WikiLeaks network.Surely the Wall Street Journal could investigate and find out the names of the Australian "library", the French foundation and the US 501C3s ?
"We're registered as a library in Australia, we're registered as a foundation in France, we're registered as a newspaper in Sweden," Mr. Assange said. WikiLeaks has two tax-exempt charitable organizations in the U.S., known as 501C3s, that "act as a front" for the website, he said. He declined to give their names, saying they could "lose some of their grant money because of political sensitivities."
Mr. Assange said WikiLeaks gets about half its money from modest donations processed by its website, and the other half from "personal contacts," including "people with some millions who approach us and say 'I'll give you 60,000 or 10,000,' " he said, without specifying a currency.How have WikiLeakS.org solved the problem faced by many unincorporated voluntary organisations, who cannot get large sums of money from rich individuals or companies or trades unions etc. because these donors would become "jointly and separately liable" for any debts incurred by the voluntary organisations , and, just as importantly, vice versa i.e. the organisation could become liable for the debts or bankruptcy of these large donors.
The other big risks to rich financial donors involve the horrendously complicated and ineffective (in terms of catching real criminals and terrorists) anti-money laundering regulations and investigations, which various government bureaucracies have imposed on the financial industry, especially for foreign money transfers.
How does WikiLeakS.org provide any protection to financial donors in such cases ?
Retrieving money from the Wau Holland Foundation is a complicated task, he said. WikiLeaks must submit receipts to the foundation, which issues grants to reimburse them. Because German law requires the foundation to publicly disclose its expenditures, WikiLeaks uses "other foundations" to aggregate its bills and send them to Wau Holland, so that some of the companies WikiLeaks does business with remain anonymous, Mr. Assange said. This prevents anyone from seeing whom, for example, WikiLeaks pays for Internet infrastructure, or where that infrastructure is located.Most of the financial supporters of WikiLeakS.org would not object to salary payments for key staff, but they do demand some sort of financial accounting and transparency, which is totally lacking at the moment.
To operate, the website needs several powerful computers linked to high-speed Internet connections. WikiLeaks particularly tries to obscure payments for "basic infrastructure that could be attacked," for "servers that are engaged in source protection," and for "security engineers," Mr. Assange said.
So far, Wau Holland has distributed €50,000 ($64,000) to a WikiLeaks account in Germany, strictly in exchange for receipts, according to Daniel Schmitt, spokesman at WikiLeaks, and Hendrik Fulda, deputy board chairman of the foundation. Mr. Schmitt controls the account.
The average donation to WikiLeaks via the Wau Holland Foundation is about €20, Mr. Fulda said. The largest donation through the foundation--€10,000--arrived from a German donor after the publication of the Afghan war documents, he said, declining to reveal further details.
Mr. Schmitt said WikiLeaks needs about $200,000 a year to cover its operating expenses--mainly network fees, rent and storage costs for the sites where the servers are, and some hardware and travel expenses. Should it decide to pay salaries to its five staff members, as it is now considering, it would need about €600,000 a year, he said.
Paying salaries is a "sensitive subject," he said, noting that outsiders might question the need for them.
Mr. Fulda of the foundation said WikiLeaks needs €10,000 to €15,000 a month to maintain its Web presence. Late last year, when donors were contributing only €2,000 to €3,000 per month, WikiLeaks was struggling to survive, he said. So it shut down its website in December, leaving up only an appeal for donors to transfer money to the group via the Wau Holland Foundation. Soon, donations per month increased 20-fold.Which shows how useless the anti-money laundering red tape is.
WikiLeaks reopened its website in May, but "within days ... donations dropped back to near their former level," Mr. Fulda said.
The fluctuation caught the attention of Wau Holland's banking partners including eBayInc.'s PayPal, which demanded explanations for the surge and fall in donations. "I explained it wasn't money laundering, just WikiLeaks donations," Mr. Fulda said.
A PayPal spokeswoman said the company is "still processing payments for WikiLeaks." She said that she couldn't comment further on a specific account but that in general, PayPal is required by anti-money-laundering laws and its own anti-fraud regulations to investigate accounts when they exceed certain limits."as they don't adhere to Moneybookers' standards, the agreement was terminated" - points to WikiLeakS.org lack of financial transparency as being a major problem.
WikiLeaks has tried to diversify away from PayPal by adding other payment options to its site, including Flattr.com, a payment system based in Sweden, and Moneybookers, a system based in the U.K.
A spokeswoman for Moneybookers said the company used to provide services to WikiLeaks but "as they don't adhere to Moneybookers' standards, the agreement was terminated." She declined to comment further. Flattr didn't respond to a request for comment.
Note also that another online money payment system which WikiLeakS.org has used during their dispute with PayPal, called TipIt.to seems to have gone "tits up" at the end of February 2010 due to "fraudulent transactions"
http://blog.tipit.to/2010/04/gesloten-voor-preventie-%E2%80%94%C2%A0closed-for-prevention/
Write to Jeanne Whalen at jeanne.whalen@wsj.com and David Crawford at david.crawford@wsj.com
We have criticised the WikiLeakS.org core activists for their abuse of the https://twitter.con/wikileaks Twitter feed before. They use it in broadcast mode, making allegations which cannot be backed up with any detail in a short 160 character tweet.
Twitter is clearly unsuitable for the accusations and counter-accusations between the Pentagon and WikiLeakS.org, about who did or did not contact whom over the Afghan War Diary messages.
Similarly the denials and media storm over the accusation and Arrest In Absentia over alleged rape in Sweden and the rapid about turn by the Swedish State Prosecutor was made worse by this "anonymous" twitter feed.
WikiLeakS.org have not shown any evidence that "the Pentagon" orchestrated the now dropped rape allegation, a claim which is specifically denied by the Swedish Prosecution Authority.
The WikiLeakS.org activists, who increasingly resemble a dodgy religious cult, have plenty of other enemies, not associated with the US Military, who could have been behind such allegations, or it could have simply a "normal" media celebrity / tabloid press "story" - where is the evidence that is must have been organised, only the US Military ? Judging from some of the malicious emails which we have received through the incompetence of some of the people who hate WikiLeakS.org, there are plenty of individuals who would be prepared to smear Julian Assange, without any prompting from any organization.
However that has not stopped the Twitter feed from being used to make that unfounded "Pentagon smear" allegation and also to to link it to the previously leaked document which the WikiLeakS.org team have prefaced with their own conspiracy theory propaganda interpretation
http://file.wikileaks.org/file/us-intel-wikileaks.pdf
If you actually bother to read that document, it simply points out the obvious, that
This old intelligence risk analysis document does not provide evidence of an actual US military plan to "destroy Wikileaks" and it certainly makes no mention at all of any "dirty tricks" as a viable option to contain the problems which Wikileaks poses to the US Military.
It is stupid of the WikiLeakS.org people to spin such conspiracy theories via their "official" Twitter feed, as doing so loses them journalistic credibility.
Twitter could be used to point people to Digitally Signed Press Releases or web site published statements such as that on the misnamed "Official WikilLeakS,org blog" http://blog.wikileaks.org/ (which does not permit even moderated comments and so is not really a blog), which contains just 3 entries in the July / August 2010 time period, when there have been about 300 tweets.
The end result is that WIkiLeakS.org and / or Julian Assange give the impression of being secretive, arrogant, control freaks, every bit as bad as the government bureaucrats, politicians and media spin doctors who they claim to be trying to expose.
Twitter is clearly unsuitable for the accusations and counter-accusations between the Pentagon and WikiLeakS.org, about who did or did not contact whom over the Afghan War Diary messages.
Similarly the denials and media storm over the accusation and Arrest In Absentia over alleged rape in Sweden and the rapid about turn by the Swedish State Prosecutor was made worse by this "anonymous" twitter feed.
WikiLeakS.org have not shown any evidence that "the Pentagon" orchestrated the now dropped rape allegation, a claim which is specifically denied by the Swedish Prosecution Authority.
The WikiLeakS.org activists, who increasingly resemble a dodgy religious cult, have plenty of other enemies, not associated with the US Military, who could have been behind such allegations, or it could have simply a "normal" media celebrity / tabloid press "story" - where is the evidence that is must have been organised, only the US Military ? Judging from some of the malicious emails which we have received through the incompetence of some of the people who hate WikiLeakS.org, there are plenty of individuals who would be prepared to smear Julian Assange, without any prompting from any organization.
However that has not stopped the Twitter feed from being used to make that unfounded "Pentagon smear" allegation and also to to link it to the previously leaked document which the WikiLeakS.org team have prefaced with their own conspiracy theory propaganda interpretation
https://twitter.com/wikileaks/status/21822519941U.S. Intelligence planned to destroy WikiLeaks, 18 Mar 2008
Reminder: US intelligence planned to destroy WikiLeakS as far back as 2008 http://bit.ly Retweeted by 100+ people
Sun Aug 22 11:09:17 +0000 2010
http://file.wikileaks.org/file/us-intel-wikileaks.pdf
If you actually bother to read that document, it simply points out the obvious, that
(U//FOUO) Web sites such as Wikileaks.org use trust as a center of gravity by protecting the anonymity and identity of the insiders, leakers, or whistleblowers. The identification, exposure, termination of employment, criminal prosecution, legal action against current or former insiders, leakers, or whistleblowers could potentially damage or destroy this center of gravity and deter others considering similar actions from using the Wikileaks.org Web site.which is something which also applies equally to the Private Banking industry etc. as it does to the US Military.
This old intelligence risk analysis document does not provide evidence of an actual US military plan to "destroy Wikileaks" and it certainly makes no mention at all of any "dirty tricks" as a viable option to contain the problems which Wikileaks poses to the US Military.
It is stupid of the WikiLeakS.org people to spin such conspiracy theories via their "official" Twitter feed, as doing so loses them journalistic credibility.
Twitter could be used to point people to Digitally Signed Press Releases or web site published statements such as that on the misnamed "Official WikilLeakS,org blog" http://blog.wikileaks.org/ (which does not permit even moderated comments and so is not really a blog), which contains just 3 entries in the July / August 2010 time period, when there have been about 300 tweets.
The end result is that WIkiLeakS.org and / or Julian Assange give the impression of being secretive, arrogant, control freaks, every bit as bad as the government bureaucrats, politicians and media spin doctors who they claim to be trying to expose.
Despite the clear warning where our email address is listed on this blog, some stupid people still think that they can email Death Threats against Julian Assange or "WikiLeakS.org" people in general to our email address, which is not associated with the WikiLeakS.org project.
Such Death Threats are:
a) Against the Acceptable Use Policy and legal Terms and Conditions of your contract with your Internet Service Provider and with your Email Provider.
b) Actually an extraditable Criminal Offence in many legal jurisdictions, with a penalty of up to 10 years in prison, regardless of any US First Amendment rights to free speech.
N.B.. this blog is not published in the USA
For example
If anything ever does happen to Julian Assange or to "Daniel Schmidt", guess who is going to be one of the prime suspects in a criminal investigation ? You are.
Such Death Threats are:
a) Against the Acceptable Use Policy and legal Terms and Conditions of your contract with your Internet Service Provider and with your Email Provider.
b) Actually an extraditable Criminal Offence in many legal jurisdictions, with a penalty of up to 10 years in prison, regardless of any US First Amendment rights to free speech.
N.B.. this blog is not published in the USA
For example
Return-Path: <6937toni@att.net>Note to "matthew brian" this blog post will continue to "name and shame" you in perpetuity via Google searches etc., unless and until you apologise and promise to donate, say 50 US Dollars to a suitable Afghan war charity.
[...]
Received: from [216.252.122.217] by n70.bullet.mail.sp1.yahoo.com with NNFMP; 12 Aug 2010 22:57:51 -0000
Received: from [98.136.44.161] by t2.bullet.sp1.yahoo.com with NNFMP; 12 Aug 2010 22:57:51 -0000
Received: from [127.0.0.1] by omp602.mail.sp1.yahoo.com with NNFMP; 12 Aug 2010 22:57:51 -0000
X-Yahoo-Newman-Property: ymail-3
X-Yahoo-Newman-Id: 535606.88313.bm@omp602.mail.sp1.yahoo.com
Received: (qmail 22479 invoked by uid 60001); 12 Aug 2010 22:57:51 -0000
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed; d=att.net; s=s1024; t=1281653871; bh=zUcr6UWVDz/czDZ+s6/tlx5dh5iM8eYiAT98vHkAbhA=; h=Message-ID:X-YMail-OSG:Received:X-Mailer:Date:From:Subject:To:MIME-Version:Content-Type; b=Dfurk3CA1fukItexIw4V8JQBOBZqWll2jsN/RLrJPil6cEzuMt3QwZgQp3GlVg1pP5dWeXrAf1jo4QSq9P5YqWFBhxj3sk7sLqmst2CLMp9QMJjnqqMpwr6OrettxdZBhp9Q85Rrpe2DSDbPRoS0ZqTI5XEZDj+K4V9V8WurmZM=
DomainKey-Signature:a=rsa-sha1; q=dns; c=nofws;
s=s1024; d=att.net;
h=Message-ID:X-YMail-OSG:Received:X-Mailer:Date:From:Subject:To:MIME-Version:Content-Type;
b=CiDeFee9Q3RaA3WqaQ0zrJIaklXILdYDCrmbA7w7vsd+USQTeJulc2eBksRQiCJjpjCTrmKqaThPWL4BbE5JqaGOj88vk39y8JQa9mtR1evw/5EQlj6P3sZkD0IexNVZNG8Oz91HO/pBV9xvIgXvnp7MUfq2UTU+bG6TXleM9G8=;
Message-ID: <343637.22380.qm@web180709.mail.sp1.yahoo.com>
X-YMail-OSG: 0dC7GrwVM1lYcTUBc0iJmotaTJq1ZrKUnC.B56i8kFB9hsr
7M5otKAfuDpnmqpmi76m7iqdTTd53yYC8xwj_zk5NIs4.P_jvZ14XDw1hAVx
WVbdIWU2yInRHewkCpX4BzWJ3RmkQe2cUjY8OT4uR5faYk88wI87bokG0QCQ
X26Jk9DrlJSUIm91iJM2bRgM9FZ1XoYNvy.UQW1weAvl9KYyxOKzmNeD5dVm
M6KZ6KU34cxeJx0UMIFRVz6YRaakpDw1Tz.W1TP9cv2qH_6n84gKlC4NzKGA
-
Received: from [75.13.166.150] by web180709.mail.sp1.yahoo.com via HTTP; Thu, 12 Aug 2010 15:57:50 PDT
X-Mailer: YahooMailRC/470 YahooMailWebService/0.8.105.279950
Date: Thu, 12 Aug 2010 15:57:50 -0700 (PDT)
From: matthew brian <6937toni@att.net>
Subject: assange
To: blog@WikiLeak.org
It may will take me some time to find this creep and when I meet him face to
face the only and last thing he will see will be the barrel of a 45 cal. colt
thsat will swipe of the smirl of this creeps face permanently and the same
goes for the creep in berlin, he is a littel easire to find because we already
know where he leaves. SEE YOU VERY SOON
If anything ever does happen to Julian Assange or to "Daniel Schmidt", guess who is going to be one of the prime suspects in a criminal investigation ? You are.
Instead of rebuilding their insecure SIPRENET infrastructure, their personnel security vetting procedures or their systems for handling Confidential Human Intelligence Sources, the US Army appears to be stupidly harassing WikiLeakS.org associates, or even people merely suspected of being associated with WikiLeakS.org i.e. "shoot the messenger"...
CNET report
The fact that there were US Army investigators present makes a nonsense of any claim that this was a "random security search".
What happened to the 4th Amendment to the US Constitution ?
Nobody who lives in a free society should tolerate being interrogated about their political opinions by Government bureaucrats or military officials. They are meant to protect freedom of speech and freedom of association, not to collaborate with our enemies by infringing or destroying these rights and freedoms.
The New York Times reports:
Is the US Army also keeping , say, New York Times journalists under surveillance ?
Which other tentacles of the vast, competing US military / security bureacratic empires (comparable to the Russian Siloviki) as outlined recently by the Washington Post Top Secret America articles, are also involved in operations against WikiLeakS.org and against their associates, readers and potential whistleblower sources around the world ?
Is everyone reading this independent WikiLeak.org blog (no "s") also unfairly regarded as a suspect ?
CNET report
July 31, 2010 4:16 PM PDTThere is obviously no evidence that Jacob Appelbaum has committed any crimes,
Researcher detained at U.S. border, questioned about Wikileaks
by Elinor Mills
LAS VEGAS -- A security researcher involved with the Wikileaks Web site was detained by U.S. agents at the border for three hours and questioned about the controversial whistleblower project as he entered the country on Thursday to attend a hacker conference, sources said on Saturday.
He was also approached by two FBI agents at the Defcon conference after his presentation on Saturday afternoon about the Tor Project.
Jacob Appelbaum, a Seattle-based programmer for the online privacy protection project called Tor, arrived at the Newark, New Jersey, airport from Holland flight Thursday morning when he was pulled aside by customs and border protection agents who told him he was randomly selected for a security search, according to the sources familiar with the matter who asked to remain anonymous.
Appelbaum, a U.S. citizen, was taken into a room, frisked and his bag was searched. Receipts from his bag were photocopied and his laptop was inspected but it's not clear in what manner, the sources said. Officials from the Immigration and Customs Enforcement and the U.S. Army then told him he was not under arrest but was being detained, the sources said. They asked questions about Wikileaks, asked for his opinions about the wars in Iraq and Afghanistan and asked where Wikileaks founder Julian Assange is, but he declined to comment without a lawyer present, according to the sources. He was not permitted to make a phone call, they said.
After about three hours, Appelbaum was given his laptop back but the agents kept his three mobile phones, sources said.
[...]
The fact that there were US Army investigators present makes a nonsense of any claim that this was a "random security search".
What happened to the 4th Amendment to the US Constitution ?
Nobody who lives in a free society should tolerate being interrogated about their political opinions by Government bureaucrats or military officials. They are meant to protect freedom of speech and freedom of association, not to collaborate with our enemies by infringing or destroying these rights and freedoms.
The New York Times reports:
Army Broadens Inquiry Into WikiLeaks DisclosureThe reported attempt recruit a paid informant associated with Wikileaks, appears to be rather inept and counterproductive.
By ELISABETH BUMILLER
Published: July 30, 2010
WASHINGTON -- Army investigators are broadening their inquiry into the recent disclosure of classified military information to include friends and associates who may have helped the person they suspect was the leaker, Pfc. Bradley Manning, people with knowledge of the investigation said Friday.
Two civilians interviewed in recent weeks by the Army's criminal division said that investigators were focusing in part on a group of Private Manning's friends and acquaintances in Cambridge, Mass. Investigators, the civilians said, apparently believed that the friends, who include students from the Massachusetts Institute of Technology and Boston University, might have connections to WikiLeaks, which made the documents public.
It is unclear whether the investigators have specific evidence or are simply trying to determine whether one person working alone could have downloaded and disseminated tens of thousands of documents.
[...]
One of the civilians interviewed by the Army's criminal division, who asked for anonymity so that his name would not be associated with the inquiry, said Friday that the investigators' questions led him to believe that the Army was concerned that there were classified documents in the Boston area.
"I was under the impression that they believed that perhaps Bradley had used friends in Cambridge as a mechanism for moving documents," he said.
The civilian also said that the Army had offered him "a considerable amount of money if I were to keep my ear to the ground and be an in with them with WikiLeaks." He said that he had turned the Army down and that he had no connection to WikiLeaks. The other civilian also said in an interview on Friday that he had no connection to WikiLeaks.
The first civilian said it appeared from the questioning that Army investigators "are trying to build a network among Bradley's friends to infiltrate WikiLeaks."
[...]
Is the US Army also keeping , say, New York Times journalists under surveillance ?
Which other tentacles of the vast, competing US military / security bureacratic empires (comparable to the Russian Siloviki) as outlined recently by the Washington Post Top Secret America articles, are also involved in operations against WikiLeakS.org and against their associates, readers and potential whistleblower sources around the world ?
Is everyone reading this independent WikiLeak.org blog (no "s") also unfairly regarded as a suspect ?
Are WikiLeakS.org starting to pay heed to the criticisms that there is actually information in some of their whistleblower leaked documents which may cause death or injury if published to the world immediately ?
The raw Afghan War Diary data has been given to The Guardian in the UK , The New York Times in the USA and Der Spiegel in Germany to analyse. and to publish at the same time.
Each of these mainstream media publications and WikiLeakS.org themselves has published extracts and summaries of the data, including "value added" conversions of the data, glossaries of obscure military acronyms and jargon and conversion of the latitude and longitude data into formats easy to feed into mapping software such as Google Earth.
WikileLeakS.org have decided to actually publish this large amount of data on the actual WikiLieakS.org website itself this time, unlike the separate Apache helicopter video www.collateralmurder.com website.
However, for WikiLeakS.org, this is a revolutionary change to their previous "information must be set free, for maximum hype and impact, regardless of the consequences to individual people" policy.
WikileakS.org also seem to have abandoned, for these Afghan War Diary pages at least, the BitTorrent and Magnet links, which they added to previous leaked document pages.
You can only download the compressed files directly over an unencrypted web connection (still no SSL/TLS or Tor Hidden Service fro reading and downloading from the website like they used to have).
There is still no way of discussing or analysing this whistleblower leak on the relevant Discussion page, which is still switched off.
WikIleakS.org still have a lot to do to protect their readers and potential analysts from being snooped on and identified by governments and other investigators.
The raw Afghan War Diary data has been given to The Guardian in the UK , The New York Times in the USA and Der Spiegel in Germany to analyse. and to publish at the same time.
Each of these mainstream media publications and WikiLeakS.org themselves has published extracts and summaries of the data, including "value added" conversions of the data, glossaries of obscure military acronyms and jargon and conversion of the latitude and longitude data into formats easy to feed into mapping software such as Google Earth.
WikileLeakS.org have decided to actually publish this large amount of data on the actual WikiLieakS.org website itself this time, unlike the separate Apache helicopter video www.collateralmurder.com website.
25th July 2010 5:00 PM EST WikiLeaks has released a document set called the Afghan War Diary, an extraordinary compendium of over 91,000 reports covering the war in Afghanistan from 2004 to 2010. [...]The US Military will, of course, not be happy that they are not in control of any such redaction and review process.
We have delayed the release of some 15,000 reports from the total archive as part of a harm minimization process demanded by our source. After further review, these reports will be released, with occasional redactions, and eventually in full, as the security situation in Afghanistan permits.
However, for WikiLeakS.org, this is a revolutionary change to their previous "information must be set free, for maximum hype and impact, regardless of the consequences to individual people" policy.
WikileakS.org also seem to have abandoned, for these Afghan War Diary pages at least, the BitTorrent and Magnet links, which they added to previous leaked document pages.
You can only download the compressed files directly over an unencrypted web connection (still no SSL/TLS or Tor Hidden Service fro reading and downloading from the website like they used to have).
There is still no way of discussing or analysing this whistleblower leak on the relevant Discussion page, which is still switched off.
WikIleakS.org still have a lot to do to protect their readers and potential analysts from being snooped on and identified by governments and other investigators.
WikiLeakS.org has a new IRC chat setup https://chat.wikileaks.org
[hat tip to IRC user "Odin" for spotting a typo in a previous reference to the old IRC system]
The new WikiLeakS.org Chat Page still claims that this is
Unless the anonymous whistleblower or potential whistleblower, takes extra precautions, then all of these systems could easily betray his or her identity, regardless of the fact that the content of what they type has been strongly encrypted.
The new IRC chat URL is now
https://chat.wikileaks.org/
or
ircs://chat.wikileaks.org:9999/wikileaks
Instead of the old self-signed Digital Certificate, which they used from January 2010 on httpps://secure.wikileaks.org:9999, they have now installed one from the same commercial Certificate Authority (GlobalSign nv-sa ) which is used for the htps://sunshinepress.org Wikileaks Upload web form
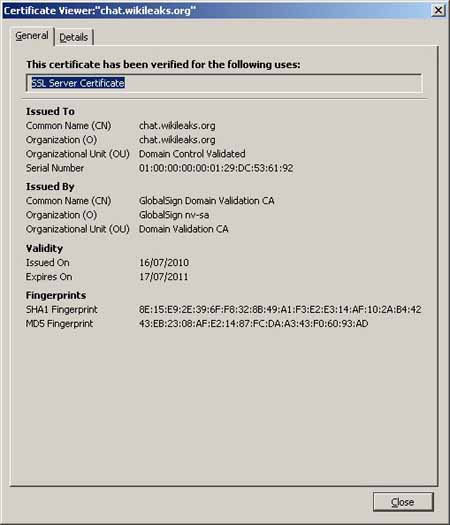
To be consistent and to help too establish trust in this Digital Certificate in case of Man--in-the-Middle attacks, WikiLeakS.org should really publish the cryptographic hash fingerprints
for this certificate, as they have done with the httpps://sunshinepess.org web pages
N.B. they should also have published the hash fingerprints on an actual WikiLeakS.org web page, since very few people will have heard of sunshinepress.org.and some of them will, correctly, be suspicious of it.
Since WikIleakS.org have not yet done so, here are the hash fingerprints for the benefit of web search engines queries:
https://chat.wikileaks.org
Serial Number: 1000000000129DC536192
SHA1: 8E:15:E9:2E:39:6F:F8:32:8B:49:A1:F3:E2:E3:14:AF:10:2A:B4:42
MD5: 43:EB:23:08:AF:E2:14:87:FC:DA:A3:43:F0:60:93:AD
IRC should not really be the primary method of contacting the WiiKiLeakS.org technical staff.
[hat tip to IRC user "Odin" for spotting a typo in a previous reference to the old IRC system]
The new WikiLeakS.org Chat Page still claims that this is
(also good for safe interviews with anonymous sources).which is simply not true of IRC or any other "live" chat or messaging system which is likely to be subjected to Communications Traffic Data Analysis by intelligence or law enforcement agencies.
Unless the anonymous whistleblower or potential whistleblower, takes extra precautions, then all of these systems could easily betray his or her identity, regardless of the fact that the content of what they type has been strongly encrypted.
The new IRC chat URL is now
https://chat.wikileaks.org/
or
ircs://chat.wikileaks.org:9999/wikileaks
Instead of the old self-signed Digital Certificate, which they used from January 2010 on httpps://secure.wikileaks.org:9999, they have now installed one from the same commercial Certificate Authority (GlobalSign nv-sa ) which is used for the htps://sunshinepress.org Wikileaks Upload web form
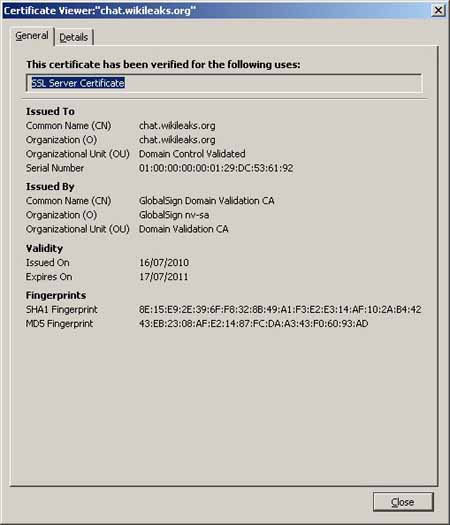
To be consistent and to help too establish trust in this Digital Certificate in case of Man--in-the-Middle attacks, WikiLeakS.org should really publish the cryptographic hash fingerprints
for this certificate, as they have done with the httpps://sunshinepess.org web pages
N.B. they should also have published the hash fingerprints on an actual WikiLeakS.org web page, since very few people will have heard of sunshinepress.org.and some of them will, correctly, be suspicious of it.
Since WikIleakS.org have not yet done so, here are the hash fingerprints for the benefit of web search engines queries:
https://chat.wikileaks.org
Serial Number: 1000000000129DC536192
SHA1: 8E:15:E9:2E:39:6F:F8:32:8B:49:A1:F3:E2:E3:14:AF:10:2A:B4:42
MD5: 43:EB:23:08:AF:E2:14:87:FC:DA:A3:43:F0:60:93:AD
IRC should not really be the primary method of contacting the WiiKiLeakS.org technical staff.
WikiLeakS.org again has a Tor Hidden Service for encrypted anonymised uploads - http://suw74isz7wqzpmgu.onion/ over 7 months after the previous one was abandoned.
The Official Tor "Blog" , which does not accept any comments or feedback from the public, has this report of the Keynote Speech given on behalf of Julian Assange at the HOPE hackers' conference in New York, by Jacob Appelbaum.
The usual rumours abound that there were FBI or other US Government Agents waiting to arrest / "talk" to him at this conference, but why they would wait until then and not do so as he came through US Passport Control is never explained by the media.
There is also a very rare, very brief, status report about the WikiLeakS.org website infrastructure:
Although slow, a Tor enabled session (download and install the software from https://www.torproject.org/easy-download.html.en) does End to End Encryption between your Web Browser and three randomly chosen Tor relay servers in the Tor anonymity cloud, almost certainly some or all of which will be in foreign countries.
The final 4th hop to the Tor Hidden Service is also encrypted.
More importantly Tor makes Communications Traffic Data Analysis very much harder , even for well resource opponents like Government intelligence agencies (who obviously also make use it themselves)
It just looks and feels like another creepy hidden visitor tracking system, even if it is not meant to be that.
If they had not disabled the SSL version of the website, then there would already have protection against sending HTTP_REFERER environment variables to the external web pages which are linked to in the WIkI. Similarly if people do not simply click on a link, but Open in a New Tab or New Window, especially in the Private Browsing modes of most modern web browsers, then this information is not sent anyway.
Please do not make it a Twitter interface !
Why not publish a high level description of this architecture, so that WikiLeakS.org can be advised on how not to make elementary mistakes, again.
Until they do so, their hopes for lots of local versions of WikiLeakS.org to spring up organically around the world in parallel, will be still born.
Is there really someone lurking in the IRC chat room 24 / 7 ?
We can dream that they will publish some PGP keys....
There is also the whole question of anonymous Mobile Phone Communications. Many more people have access to these than to fast computers and internet connections.
Surely the WikiLeakS.org technical team should be creating or promoting mobile phone SMS text and MMS message anonymous submissions systems ?
The Official Tor "Blog" , which does not accept any comments or feedback from the public, has this report of the Keynote Speech given on behalf of Julian Assange at the HOPE hackers' conference in New York, by Jacob Appelbaum.
The usual rumours abound that there were FBI or other US Government Agents waiting to arrest / "talk" to him at this conference, but why they would wait until then and not do so as he came through US Passport Control is never explained by the media.
There is also a very rare, very brief, status report about the WikiLeakS.org website infrastructure:
HOPE 2010 Talk / Current statusWithout telling anybody and without establishing a link of trust between the two domain names (see our previous blog article)
Hello,
Jacob Appelbaum is speaking today on behalf of the project at the HOPE2010 conference. He will cover past, present and future developments of the project. For further information please visit the conference website: http://www.thenexthope.org/.
Now some general NEWS.
The submission system is up and running again (yes also reachable via Tor for those that do not trust SSL). Some important changes that you should be aware of:
* we moved the location of the submission system to https://sunshinepress.org/
* The tor submission path uses a new hidden service address located at http://suw74isz7wqzpmgu.onion/Some good news at last !
Although slow, a Tor enabled session (download and install the software from https://www.torproject.org/easy-download.html.en) does End to End Encryption between your Web Browser and three randomly chosen Tor relay servers in the Tor anonymity cloud, almost certainly some or all of which will be in foreign countries.
The final 4th hop to the Tor Hidden Service is also encrypted.
More importantly Tor makes Communications Traffic Data Analysis very much harder , even for well resource opponents like Government intelligence agencies (who obviously also make use it themselves)
SSL for the other services like the websites will take some more time until it is available.What is so difficult about purchasing and installing another Digital Certificate to replace the old one, before making other changes to the infrastructure ?
Those users that do not like to install a generic IRC client can use the webchat again which is located at https://chat.wikileaks.org/ and connects to our internal IRC server. We added some additional means of protection to the IRCd to prevent the leakage of users identities.This IRC chat system is all very well for reporting errors on the website etc. but is is absolutely not suitable for preserving the anonymity of potential whistleblowers.
The archive is now back for some time and we are still working on it. The most visible changes so far are the support for torrents and magnet links for files referenced in the archive, a facelift of the design, content cleanup. Public edits are still disabled but will be enabled again. Public comments will be disabled until we have an appropriate solution in place. We removed some stuff to hide the identities of the users working on the wiki as well as protecting the identity of people visiting the site. For example external links always use a trampoline now to make sure that 3rd party sites do not know where you came from. Furthermore we deleted all accounts not used for a year as part of the cleaning process.We have meant to comment on the "trampoline" before. Why did they waste their time with this feature ?
It just looks and feels like another creepy hidden visitor tracking system, even if it is not meant to be that.
If they had not disabled the SSL version of the website, then there would already have protection against sending HTTP_REFERER environment variables to the external web pages which are linked to in the WIkI. Similarly if people do not simply click on a link, but Open in a New Tab or New Window, especially in the Private Browsing modes of most modern web browsers, then this information is not sent anyway.
Generally the technical staff is pretty busy putting the resources you granted us to good use. We are still extending the network with new machines, but will provide a dedicated interface for this type of help soon (email just does work for this kind of task).Should this read "email just does not work for this kind of task" ?
Please do not make it a Twitter interface !
We have switched the complete system to a new architecture.What was wrong with the old one ? Did it not scale properly ?
Why not publish a high level description of this architecture, so that WikiLeakS.org can be advised on how not to make elementary mistakes, again.
Until they do so, their hopes for lots of local versions of WikiLeakS.org to spring up organically around the world in parallel, will be still born.
If you notice that something does not work as expected please drop into the chat and talk to the staff there.WikiLeakS.org has a world wide audience.
Is there really someone lurking in the IRC chat room 24 / 7 ?
They will be able to either relay your message or get you in contact with someone who can look at the problem.We are glad that someone is trying to sort out the technological mess that the WikiILeakS.org project deteriorated into.
The WL teams want to thank everybody for their support and patience.
By WikiLeaks on July 17, 2010
We can dream that they will publish some PGP keys....
There is also the whole question of anonymous Mobile Phone Communications. Many more people have access to these than to fast computers and internet connections.
Surely the WikiLeakS.org technical team should be creating or promoting mobile phone SMS text and MMS message anonymous submissions systems ?
No comments:
Post a Comment